Tech Giants Targeted with over 5000 Dependency Confusion Copycats
Dependency Confusion - A trending threat to cybersecurity
TL;DR
Sonatype recently reported that Amazon, Zillow, Slack, and Lyft (among others) recently were targeted by malicious dependency confusion copycats; the same codes have been identified inside the npm public repository housing sensitive pieces of information.
A software vendor has deemed this catastrophe a result of the Python Package Installer's default process, which leaves the software development process exposed to dependency confusion attacks.

Key Facts
The unconventional decision by the security researcher Alex Birsan to put private repository material inside the npm public repository played a major role.
The PyPi packages seemed free of malicious codes - a bold and shocking wake-up call to the software development organization.
Other companies like Qentinel found unidentified libraries in their space - this means 'dependency confusion' is a bigger threat than most think.
The Python Package Index is fundamentally insecure.
Details
Microsoft hired researchers to attack itself over growing concerns of the grueling growth of these attacks. Most giants' attacks were horrendous, but it remains unknown if they succeeded in executing malware inside their networks. PyPi, npm, and RubyGems open source code repositories, however, have been hit with over 5000 of these packages in their servers.
These attacks have been all over the place since Birsan published his discoveries on them. After being hit by a related attack printed from Birsan's unauthorized and unconventional test in its servers, Microsoft recently fell to another attack by hired researchers from Contrast.
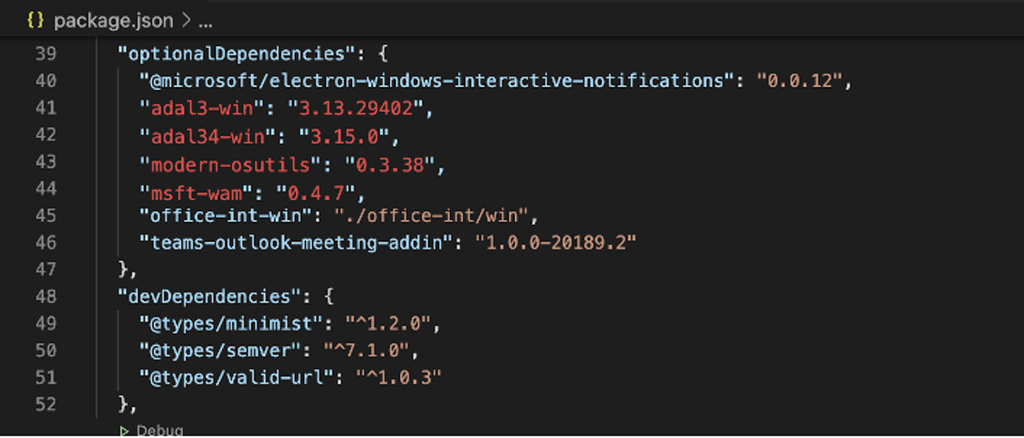
At Contrast, the Director of the security team, Matt Austin, mentioned starting by looking into dependencies in the Microsoft Team applications. He mentioned a JavaScript package, "Optional Dependencies," he then made a Microsoft team's development machine download and ran a package he uploaded on npm. The package also employed the name of a module listed as an optional dependency.
History is familiar with these attacks, but this one has a slightly different but inconspicuous paradigm. Some names didn't exist on the npm registry at the time of development.
In recent times, many developers at small or scaly enterprises use package installers to download and import libraries, assemble them to create an app offered to customers or utilized them internally at the company.
But some of these apps contain sensitive codes, depending on their nature. After building, companies tend to mix private with public libraries downloaded for public portals like npm, PyPi, etc.
It's been discovered that if vigilante actors get their hands on private libraries' names, they could register these names on public libraries that contain dangerous codes and eventually upload them on public portals.
Taking this path, researchers reported that they successfully loaded their innocuous code inside the repositories employed by 35 major tech firms, names including major firms like Apple, Microsoft, Netflix, Shopify, Uber, and of course, 30 more.
The private repositories that have been spotlighted under the radar are npm, PyPi, and RubyGems, but researchers have determined that JFrog and NuGet's package managers are also exposed.
Microsoft has suggested companies should analyze their internal package reports. Some companies have thrust this issue aside, but Microsoft seems to have a clearer grasp of the issue's understanding.
Get similar news in your inbox weekly, for free
Share this news:
Latest stories
Best Cloud Hosting in the USA
This article explores five notable cloud hosting offers in the USA in a detailed way.
Best Dedicated Hosting in the USA
In this article, we explore 5 of the best dedicated hosting providers in the USA: …
The best tools for bare metal automation that people actually use
Bare metal automation turns slow, error-prone server installs into repeatable, API-driven workflows by combining provisioning, …
HIPAA and PCI DSS Hosting for SMBs: How to Choose the Right Provider
HIPAA protects patient data; PCI DSS protects payment data. Many small and mid-sized businesses now …
The Rise of GPUOps: Where Infrastructure Meets Thermodynamics
GPUs used to be a line item. Now they're the heartbeat of modern infrastructure.
Top Bare-Metal Hosting Providers in the USA
In a cloud-first world, certain workloads still require full control over hardware. High-performance computing, latency-sensitive …
Top 8 Cloud GPU Providers for AI and Machine Learning
As AI and machine learning workloads grow in complexity and scale, the need for powerful, …
How ManageEngine Applications Manager Can Help Overcome Challenges In Kubernetes Monitoring
We tested ManageEngine Applications Manager to monitor different Kubernetes clusters. This post shares our review …
AIOps with Site24x7: Maximizing Efficiency at an Affordable Cost
In this post we'll dive deep into integrating AIOps in your business suing Site24x7 to …
A Review of Zoho ManageEngine
Zoho Corp., formerly known as AdventNet Inc., has established itself as a major player in …