7 Static Analysis Tools to Secure and Build Stable Kubernetes Clusters
in DevOps , Kubernetes

Securing your Kubernetes resources starts from scanning your YAML manifest for potential security threats before deploying them into a cluster.
The tools highlighted in this article will help you scan, analyze, and recommend best practices to help you achieve a secure and stable Kubernetes environment.
Static code analysis in Kubernetes is a necessary procedure that often determines the lifetime security of our application. Kubernetes YAML manifest is the source code file that contains all information about our application before deploying it to a cluster. The security checks we apply to this file directly affect the health of our application after it is deployed.
By analyzing the code from the early stage, we can identify security threats and fix them before deploying. And to make this process easier, automated, and efficient, we need to leverage some Kubernetes security tools built for this purpose.
In this article, we’ll look at seven of the best open-source Kubernetes static code analysis tools that can help developers build secure and stable Kubernetes clusters.
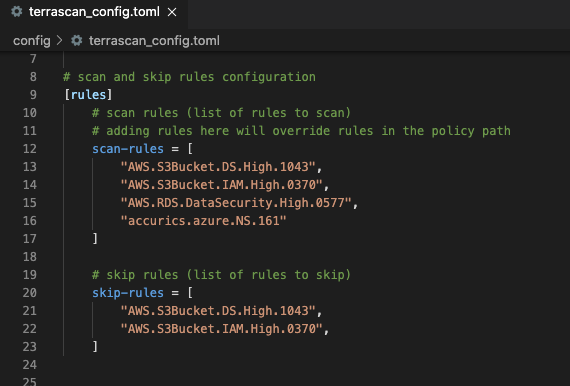
Terrascan from Accurics
Terrascan ensures security in Kubernetes, Terraform, and AWS CloudFormation by checking compliance with CIS security best practices. It scans your Kubernetes cluster and compares it with over 500 standard security policies, which allow it to detect loopholes and vulnerabilities in your Kubernetes cluster.
Terracan is an open-source tool from Accurics that integrates well with Kubernetes, Github, and major cloud platforms, including AWS, Azure, and GoogleCloud.
It can be easily integrated with your CI/CD pipeline or installed and run locally on your computer.
KubeLinter from Stackrox
KubeLinter by Stackrox is an open-source static analysis tool that scans for Kubernetes misconfigurations and security violations. It inspects Kubernetes YAML files and Helm charts and provides engineers with helpful information about the security before deploying into a cluster. It checks your Kubernetes YAML files and Helm charts against 19 security and production readiness practices and gives room to configure custom security checks.
The Golang written tool from Stackrox is an easily installed command-line utility that provides valuable feedback from the built-in security checks.
Checkov from Bridgecrew
Built by Bridgecrew, Checkov is an open-source project that helps developers build a secure code-base by finding and flagging security misconfigurations in IaC tools such as Kubernetes, Terraform, and CloudFormation. It uses graph-based scanning techniques to identify, fix issues, prevent misconfiguration, and ensure security in your Kubernetes environment.
Checkov is built on Python and provides its scan through multiple platforms, including Jenkins, CLI, JSON, and GitHub Markdown.
Krane from Appvia
Krane is a Kubernetes role-based access control (RBAC) analysis tool written in Ruby. It evaluates your Kubernetes against a set of customizable built-in RBAC rules and generates a report of potential RBAC security risks in the cluster. It can be run locally as a CI or Docker container or integrated into your CI/CD pipeline. Krane provides an intuitive dashboard that alerts and presents detected security risks in the order of severity.
Kubesec fromControlpanel.io
Kubesec is an open-source static analysis and security scanner tool for Kubernetes. It takes multiple YAML files input, scans the document, and returns the security threats fund in JSON format. The error message, security score, and reason for each score from the Kubesec test will be presented in the JSON output.
Built by controlplane.io, Kubesec and can be installed and used through the command line and Docker. It can also be used through your browser via v2.kubesec.io/scan for easy and quick security scanning.
Kube Score
Kube Score is an easy-to-use Kubernetes static analysis tool that scans Kubernetes objects directly from the browser. It analyzes Kubernetes object definitions and provides a list of suggested recommendations of things that we can do to make the cluster more secure as the output.
Kube score scans Kubernetes objects using a non-intrusive technique, and the output will be presented in a clear, readable format for easy implementation.
In addition to being quickly usable from the browser via kube-score.com, Kube score can be installed and run locally through Docker, Homebrew, or downloaded binaries for different operating systems.
Kubeaudit from Shopify
As the name denotes, Kubeaudit audits Kubernetes clusters for potential security vulnerabilities. It comes with built-in security tests called “auditors.” The auditor is a list of security tests such as whether or not there is a cluster image misconfiguration, whether or not there are loopholes that allow security escalation, or whether the root account is disabled for the system or not.
For each auditor compared against your Kubernetes resources, Kubeaudit provides comprehensive detail of any detected error and recommends security best practices for your Kubernetes cluster.
Which of These Static Analysis Tools Should I Choose?
The Kubernetes static analysis tool you should choose and when to choose it depends on what security check you want to do. Whether you only want to scan and detect security misconfigurations in your Kubernetes YAML manifest before deploying to a cluster, or you want to analyze an already running Kubernetes cluster for potential security risks.
Terrascan, Kubelinter, and Checkov can scan the YAML manifest and against specific in-built rules they have configured. These tools essentially perform static code analysis by checking the YAML manifest for potential security misconfiguration or areas where you can improve the security of your Kubernetes files before deploying them into a cluster.
On the other hand, full-featured security tools such as Kubesec and Kubeaudit provide a comprehensive scanning and reporting of the security status of your Kubernetes cluster. These tools go deep into the container and analyze security issues within the underlying container, and, in most cases, provide recommended and suggested fixes to the detected security issues.
Get similar stories in your inbox weekly, for free
Share this story:

The Chief I/O
The team behind this website. We help IT leaders, decision-makers and IT professionals understand topics like Distributed Computing, AIOps & Cloud Native
Latest stories
Best Cloud Hosting in the USA
This article explores five notable cloud hosting offers in the USA in a detailed way.
Best Dedicated Hosting in the USA
In this article, we explore 5 of the best dedicated hosting providers in the USA: …
The best tools for bare metal automation that people actually use
Bare metal automation turns slow, error-prone server installs into repeatable, API-driven workflows by combining provisioning, …
HIPAA and PCI DSS Hosting for SMBs: How to Choose the Right Provider
HIPAA protects patient data; PCI DSS protects payment data. Many small and mid-sized businesses now …
The Rise of GPUOps: Where Infrastructure Meets Thermodynamics
GPUs used to be a line item. Now they're the heartbeat of modern infrastructure.
Top Bare-Metal Hosting Providers in the USA
In a cloud-first world, certain workloads still require full control over hardware. High-performance computing, latency-sensitive …
Top 8 Cloud GPU Providers for AI and Machine Learning
As AI and machine learning workloads grow in complexity and scale, the need for powerful, …
How ManageEngine Applications Manager Can Help Overcome Challenges In Kubernetes Monitoring
We tested ManageEngine Applications Manager to monitor different Kubernetes clusters. This post shares our review …
AIOps with Site24x7: Maximizing Efficiency at an Affordable Cost
In this post we'll dive deep into integrating AIOps in your business suing Site24x7 to …
A Review of Zoho ManageEngine
Zoho Corp., formerly known as AdventNet Inc., has established itself as a major player in …