Fusing Linux’s eBPF with Windows
eBPF is now operable on other operating system other than Linux - Windows
TL;DR
History has it that on May 10, 2021, Microsoft announced the release of a new project that brings eBPF open source projects to Windows 10, Windows Server 2016, and eventual versions.
Key Facts
Microsoft Windows becomes the 2nd operating system to host eBPF, the first being Linux.
The ebpf-for-windows project's long-term blueprint is to bring IOVisor uBPF project and several existing eBPF projects to Windows.
At the moment, socket binding and eXpress data path (XDP) remain the only two hooks available on eBPF for Windows
Details
The acronym eBPF may come off as strange to some people, especially if they have been paying less attention to cloud native communities, Linux operating system-related posts. It has been the buzz on many conference schedules in recent years, and now it has its own conference.
Extended Berkeley Packet Filter (eBPF), also known as “God's Own Nectar,” is a popular, unique innovation that provides networking, application profiling, security, and performance troubleshooting.
eBPF debuted on December 19, 1992, developed by Steven McCanne and Van Jacobson. eBPF is an extension and a kernel-mode BPF; this started with Linux in its version 3.18. Since then, a significant amount of software and tools have taken their roots or essence around eBPF.
The eBPF community recognizes the Linux Kernel as the first OS to implement its projects; many other operating systems have plans laid out to bring eBPF to their platforms.
Not only does eBPF nowadays stand out in network filtering, analysis, and management, it extends far beyond these utility reach. Process context tracing and system call filtering are some of the capabilities developers and operators enjoy with eBPF. It’s evolved into a versatile player that can be suitable for system profiling, collecting, programming tracing, and aggregating low-end personalized metrics. eBPF has made a name for itself; security programs like Tracee, Falco, and Cilium; Kubernetes-native programs like Hubble and Pixie, the Clang toolchain, and other toolchains.
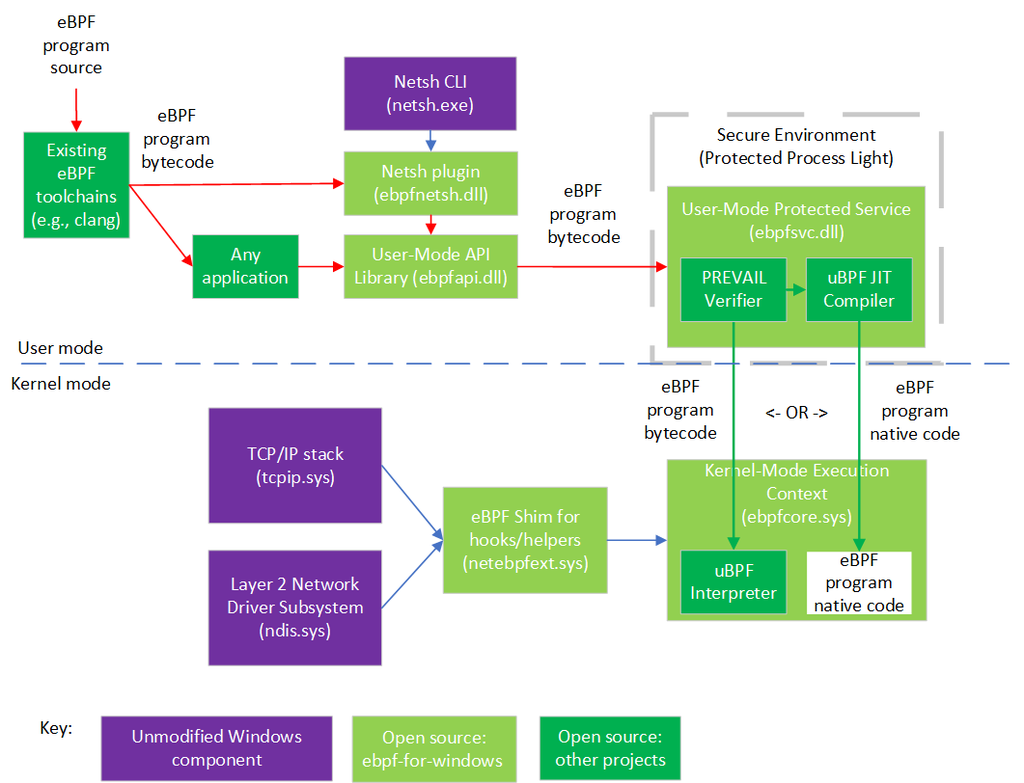
In a blog post hosted by Dave Thaler, Partner Software Engineer, and Poorna Gaddehosur, colleague and Principal Software Engineer Lead at Microsoft, Microsoft stated that “The ebpf-for-windows project aims to allow developers to use familiar eBPF toolchains and application programming interfaces (APIs) on top of existing versions of Windows. Building on the work of others, this project takes several existing eBPF open source projects and adds the “glue” to make them run on Windows.”
The long-term blueprint starts with a new open source project that lines eBPF up for integration with Windows 10 and Windows Server 2016. Subsequently, the expansion will make other eBPF open source projects like the IOVisor uBPF project and the PREVAIL verifier compatible with Windows. eBPF programs go through refining in various languages before being compiled to eBPF bytecode.
On Windows, this bytecode gets consumed utilizing a library that implements the Libbpf APIs, which is fused into a command-line tool.
There are only two hooks available in the ebpf-for-windows-project - XDP and socket bind. But with further development, more hooks, not just network hooks, will be added.
Get similar news in your inbox weekly, for free
Share this news:
Latest stories
Best Cloud Hosting in the USA
This article explores five notable cloud hosting offers in the USA in a detailed way.
Best Dedicated Hosting in the USA
In this article, we explore 5 of the best dedicated hosting providers in the USA: …
The best tools for bare metal automation that people actually use
Bare metal automation turns slow, error-prone server installs into repeatable, API-driven workflows by combining provisioning, …
HIPAA and PCI DSS Hosting for SMBs: How to Choose the Right Provider
HIPAA protects patient data; PCI DSS protects payment data. Many small and mid-sized businesses now …
The Rise of GPUOps: Where Infrastructure Meets Thermodynamics
GPUs used to be a line item. Now they're the heartbeat of modern infrastructure.
Top Bare-Metal Hosting Providers in the USA
In a cloud-first world, certain workloads still require full control over hardware. High-performance computing, latency-sensitive …
Top 8 Cloud GPU Providers for AI and Machine Learning
As AI and machine learning workloads grow in complexity and scale, the need for powerful, …
How ManageEngine Applications Manager Can Help Overcome Challenges In Kubernetes Monitoring
We tested ManageEngine Applications Manager to monitor different Kubernetes clusters. This post shares our review …
AIOps with Site24x7: Maximizing Efficiency at an Affordable Cost
In this post we'll dive deep into integrating AIOps in your business suing Site24x7 to …
A Review of Zoho ManageEngine
Zoho Corp., formerly known as AdventNet Inc., has established itself as a major player in …